Ledger Live – Secure Login Guide
Introduction to Ledger Live Secure Login
Ledger Live provides a powerful and highly secure environment for managing your digital assets. As the official companion application for Ledger hardware wallets, Ledger Live allows you to buy, sell, exchange, and stake your cryptocurrencies while maintaining complete control over your private keys. The secure login process ensures that only you, the legitimate hardware wallet holder, can access your assets. Unlike traditional online platforms, Ledger Live does not store your sensitive information on external servers. Instead, everything is safeguarded within your hardware wallet, offering unmatched security.
The login process is built around strong encryption, hardware-based verification, and user-friendly authentication steps. By connecting your Ledger device and following the app’s instructions, you can access your portfolio confidently, knowing your digital wealth is protected against online threats. This guide explores every aspect of secure login, helping you maximize your Ledger Live experience.
Why Secure Login Matters
With the rapid growth of digital currencies, cybercrime has evolved into a major threat. Hackers are constantly targeting exchanges, wallets, and unsuspecting users to steal cryptocurrencies. Unlike traditional financial systems, stolen cryptocurrencies are almost impossible to recover, making security paramount.
Ledger Live’s secure login minimizes risks by eliminating the need for passwords stored on servers. Instead, it integrates your hardware wallet directly into the authentication process. Each login requires a physical confirmation on your Ledger device, ensuring that even if a malicious actor gains access to your computer, they cannot breach your wallet without the actual device and your PIN.
Steps to Secure Login in Ledger Live
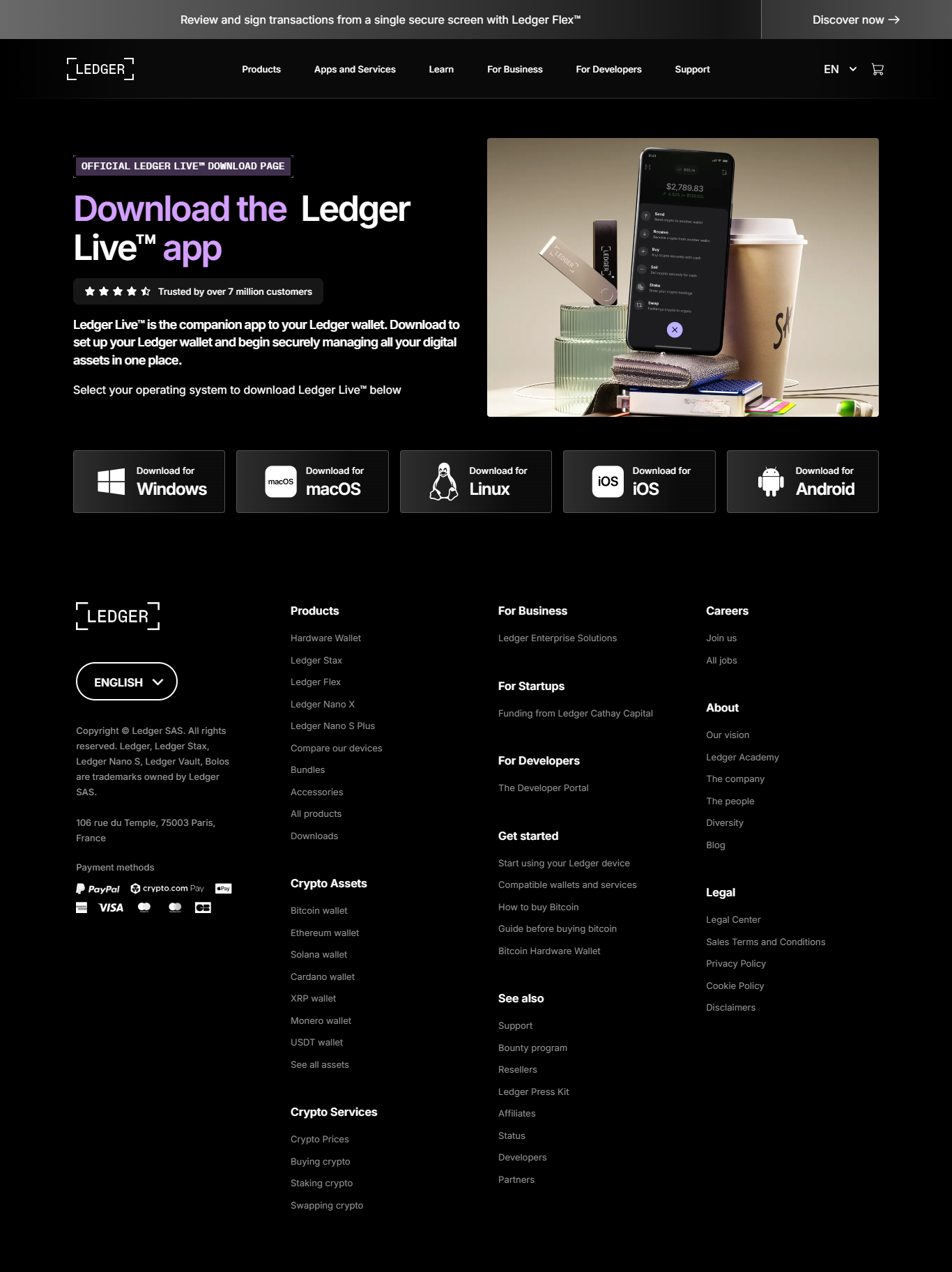
1. Install Ledger Live
Begin by downloading the official Ledger Live application from Ledger’s official website. Ensure that you avoid third-party sites, as they may host malicious software that could compromise your funds.
2. Connect Your Ledger Device
Plug your Ledger Nano S, Nano X, or Stax into your computer or connect via Bluetooth if supported. Once connected, unlock the device using your unique PIN code.
3. Open Ledger Live Application
Launch Ledger Live, and navigate to the login screen. The app will prompt you to confirm the connection between the Ledger device and the application.
4. Verify with Hardware Confirmation
On your Ledger device, review the login confirmation request. Physically approve it by pressing the device’s buttons. This additional step ensures that no unauthorized login occurs without your consent.
5. Access Your Portfolio
Once confirmed, you gain full access to your dashboard, where you can check balances, manage accounts, and perform transactions securely.
Security Features of Ledger Live Login
Ledger Live integrates multiple protective mechanisms that work together to secure your login and transaction process:
- Hardware Verification: Requires your physical Ledger device for login authentication.
- PIN Protection: Even if your device is stolen, access is denied without the correct PIN.
- Passphrase Option: Advanced users can add an additional passphrase for layered protection.
- Secure Element Chip: Your Ledger device is equipped with a certified secure chip that stores private keys safely.
- End-to-End Encryption: Communication between Ledger Live and your device is encrypted, preventing interception.
Tips for Maximizing Secure Login
While Ledger Live provides world-class security, your actions play a crucial role in maintaining account safety. Follow these best practices:
- Always download Ledger Live from the official Ledger website.
- Regularly update both Ledger Live and your device firmware for the latest security enhancements.
- Never share your recovery phrase with anyone, not even Ledger support.
- Use your Ledger device in a secure, private environment.
- Be cautious of phishing attempts and fraudulent websites imitating Ledger’s platform.
Common Login Issues and Solutions
Users sometimes encounter difficulties while logging into Ledger Live. Below are common problems and solutions:
- Device Not Recognized: Ensure drivers are installed and try using a different USB cable or port.
- Ledger Live Not Responding: Restart the application or reinstall the latest version.
- Firmware Mismatch: Update your Ledger device firmware to align with the app version.
- PIN Entry Errors: Be careful while entering your PIN; three wrong attempts will reset your device.
Conclusion
Secure login in Ledger Live is the foundation of safe cryptocurrency management. With hardware-backed verification, encryption, and user-friendly authentication steps, Ledger Live ensures that your digital wealth remains in your control. By understanding the login process and following recommended security practices, you can confidently manage your portfolio without fear of online threats.
Ledger Live is not just an application; it is your gateway to secure and convenient digital asset management. Always prioritize security, stay updated, and use your Ledger device wisely to maximize protection.